Know what your dependencies can do
Capslock analyzes your code to show which privileged operations your dependencies can access: file I/O, network calls, code execution, and more. Understand your supply chain risk before it becomes a problem.
When you add a dependency to your project, you’re trusting that code with your system’s resources. Most packages only need a fraction of what they could theoretically access, but without analysis, you can’t tell which ones punch above their weight.
Capslock traces the call graph from your dependencies through to privileged standard library functions. A logging library that can execute shell commands? A date formatter with network access? These are the signals that warrant closer inspection.
Why capabilities matter
Traditional security scanning focuses on known vulnerabilities. Capslock takes a different approach: it maps what your code can do, regardless of whether anyone has found a way to exploit it yet.
This serves several purposes:
- Understanding packages: A package’s capabilities tell you what it’s designed to do. If those capabilities don’t match the package’s stated purpose, something may be off.
- Directing review effort: When you can’t audit everything, focus on the code paths that have the most access.
- Detecting supply chain changes: A new version of a dependency that suddenly gains network access deserves scrutiny, even if no CVE exists.
The idea draws from the Principle of Least Privilege. If code only needs to parse strings, it shouldn’t have the ability to open network connections.
Example output
Running capslock in a Go project directory analyzes all dependencies and reports their capabilities:
Analyzed packages:
github.com/go-git/go-git/v5 v5.16.4
github.com/spf13/cobra v1.10.2
golang.org/x/crypto v0.47.0
golang.org/x/net v0.49.0
modernc.org/sqlite v1.44.3
... (40 more packages)
ARBITRARY_EXECUTION: 2 references
EXEC: 1 references
FILES: 2 references
NETWORK: 2 references
OPERATING_SYSTEM: 1 references
READ_SYSTEM_STATE: 2 references
REFLECT: 2 references
RUNTIME: 1 references
SYSTEM_CALLS: 2 references
UNANALYZED: 2 references
UNSAFE_POINTER: 2 references
This project uses git operations, SQLite, and makes network calls, so these capabilities make sense. The EXEC capability comes from go-git needing to shell out to git in some cases.
JCapsLock provides similar output for Java projects:
Package: org.apache.commons:commons-compress:1.24.0
Capabilities:
File System:
• CAPABILITY_FILES - File system operations
└─ ZipFile.<init> → FileInputStream.<init>
Reflection:
• CAPABILITY_REFLECT - Reflection and dynamic code
└─ ZstdUtils → Class.forName
Compare these to what Capslock found in malicious code from a 2022 supply chain attack:
CAPABILITY_EXEC: 1 calls
CAPABILITY_FILES: 1 calls
CAPABILITY_MODIFY_SYSTEM_STATE: 2 calls
CAPABILITY_NETWORK: 1 calls
CAPABILITY_OPERATING_SYSTEM: 1 calls
CAPABILITY_READ_SYSTEM_STATE: 1 calls
That’s a lot of capabilities for a small init function. The code was exfiltrating environment variables over the network and executing remote commands. A human reviewer would catch this immediately, but with thousands of lines to review in any dependency, these signals help direct attention where it matters.
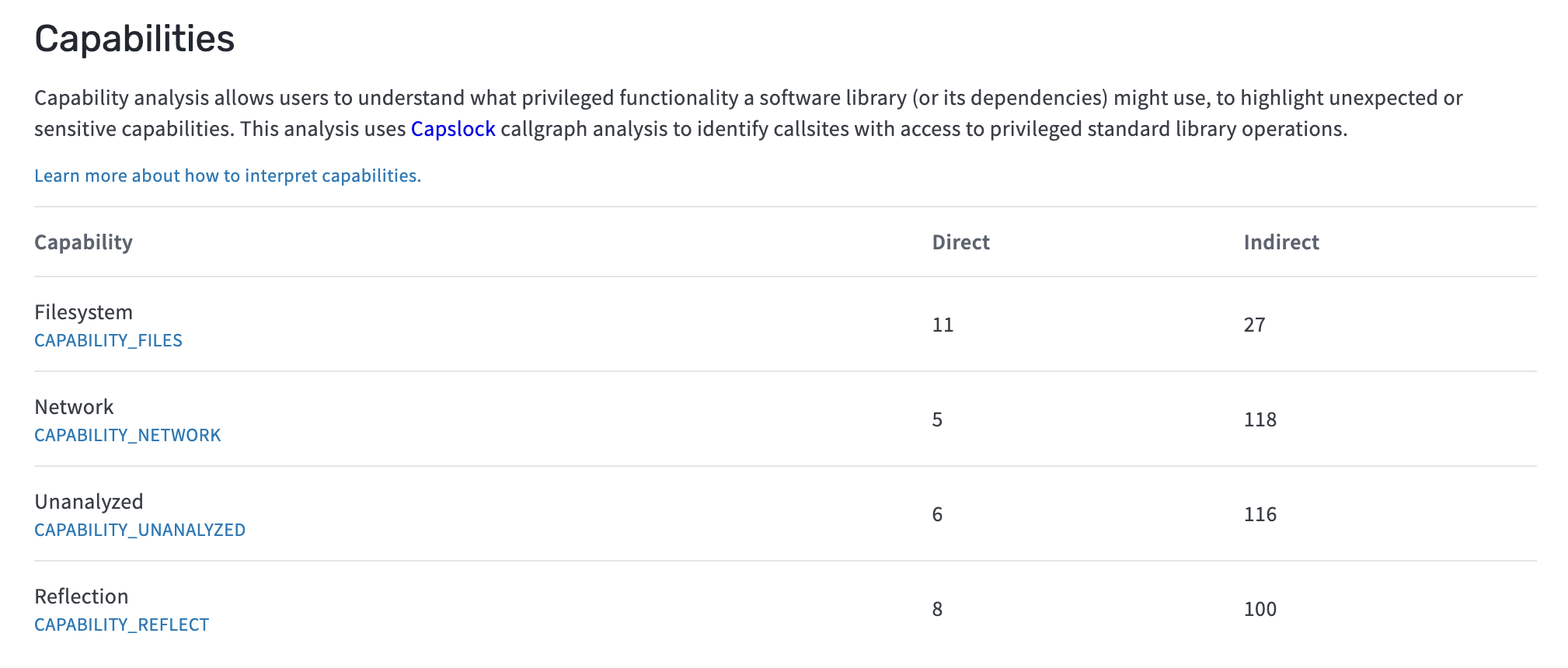
For Go packages, you can also view Capslock analysis directly on deps.dev. Google runs the analysis centrally and makes results available without any setup. Look for the “Analysis” tab on any Go package page.
Implementations
Go
The original implementation from Google. Analyzes Go packages via source code using VTA (Variable Type Analysis) for call graph construction.
github.com/google/capslockRust
Developed by the Rust Foundation with Alpha-Omega funding. Experimental analysis for Rust projects at the LLVM IR level.
github.com/rustfoundation/cargo-capslockJava
Maven plugin that analyzes bytecode. Works with any Maven package without source code. Supports capability snapshots to track changes over time.
github.com/serj/JCapsLockGetting started
Go
go install github.com/google/capslock/cmd/capslock@latest
capslock -packages ./...
Rust
The Rust implementation is still experimental. Clone the repository and build from source:
git clone https://github.com/rustfoundation/cargo-capslock
cd cargo-capslock
cargo build --release
Java
Add the plugin to your pom.xml:
<pluginRepositories>
<pluginRepository>
<id>jitpack.io</id>
<url>https://jitpack.io</url>
</pluginRepository>
</pluginRepositories>
<build>
<plugins>
<plugin>
<groupId>com.github.serj.JCapsLock</groupId>
<artifactId>mvn-capslock</artifactId>
<version><!-- see JitPack for latest --></version>
</plugin>
</plugins>
</build>
Then run:
mvn capslock:analyze
Getting involved
Each implementation has its own repository and contribution guidelines. The Go version is the most mature, while the Rust and Java implementations welcome contributors who want to help shape their direction.
If you’re interested in bringing capability analysis to another language ecosystem, the Capslock Project organization is the place to coordinate.
Acknowledgments
Capslock development has been funded by Google and Alpha-Omega, a project of the Open Source Security Foundation focused on improving open source software supply chain security.
